The African Cyberthreat Assessment Report 2024 by INTERPOL highlights how Africa’s rapid digital transformation has brought unprecedented opportunities but also heightened exposure to sophisticated cyber threats. Among these, Business Email Compromise (BEC), sextortion, and pig butchering stand out as major concerns, targeting individuals, businesses, and governments alike.
As an Ambassador for Internet Governance, I recognize the critical role we play in fostering safer Internet practices, advocating for policy changes, and strengthening international cooperation to combat these growing challenges.
Let’s explore these threats and the ways internet governance can address them.
1. Business Email Compromise (BEC): Exploiting Trust for Financial Gain
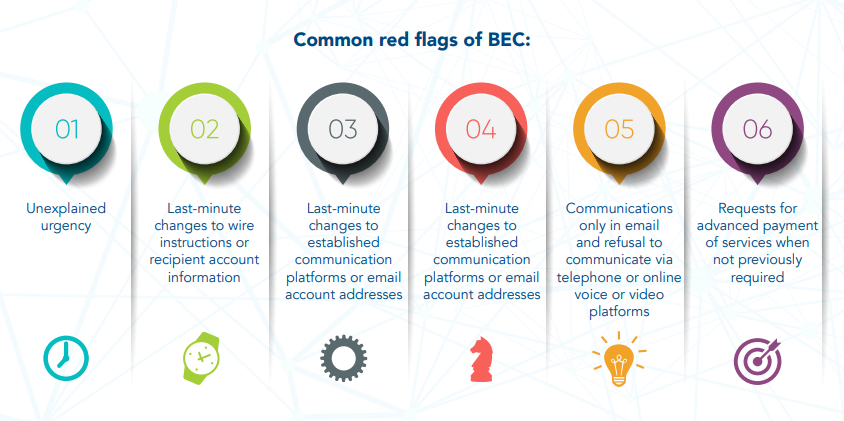
BEC is a type of cybercrime that involves the use of email fraud to attack organizations and individuals. It generally involves cybercriminals compromising legitimate business or personal email accounts through social engineering and/or computer intrusion and attempting to trick organizations and individuals into making unauthorized transfers of funds or divulging confidential information. Between April 2022 and April 2023, over 35 million BEC attempts were recorded globally, with financial losses exceeding $50 billion since 2013.
📌 Role of Internet Governance: Through Internet governance, African countries can:
- Mandate the use of email authentication protocols like SPF, DKIM, and DMARC to reduce spoofing. Follow this https://shorturl.at/lfLtl – (It’s one of my posts so it’s safe to click) – to learn more about these protocols.
- Strengthen cross-border collaboration to trace and recover stolen funds swiftly.
- Standardize BEC reporting frameworks across countries to ensure timely actions.
2. Sextortion and Catfishing: Manipulating Human Vulnerability for Blackmail
Romance scams involve fraudsters pretending to be in a romantic or close friendship for financial gain. They typically use fake online personas to build trust with victims, often through social media, messaging services, and dating apps. After establishing a connection, scammers exploit vulnerabilities to deceive or steal from the victim. Two emerging trends in romance scams in Africa are sextortion and catfishing. Catfishing involves creating fake identities using stolen photos or personal information to manipulate victims over time. Scammers build trust before making emotional pleas for money, claiming illness, injury, or other crises, and once the victim sends money, the scammer disappears, leaving the victim financially and emotionally devastated. This trend is escalating, targeting individuals ranging from young adults to high-profile executives.
📌 Role of Internet Governance: Internet governance frameworks can:
- Advocate for platforms to adopt advanced #AI detection tools to identify and block explicit content proactively.
- Facilitate quick takedown protocols for non-consensual media, empowering victims to regain control.
- Promote public awareness campaigns about online privacy, particularly targeting younger users.
📌 Engagement Question: In the context of sextortion and similar cybercrimes, should victims consider paying the blackmail demands, or is it better to refuse and face the potential exposure? Similar to ransomware attacks, where paying the ransom often doesn’t guarantee recovery, paying for the release of personal content or to maintain a perceived romantic connection may not resolve the situation. What are your thoughts on the ethical, emotional, and practical implications of such decisions?
3. Pig Butchering: The Crypto-Investment Mirage
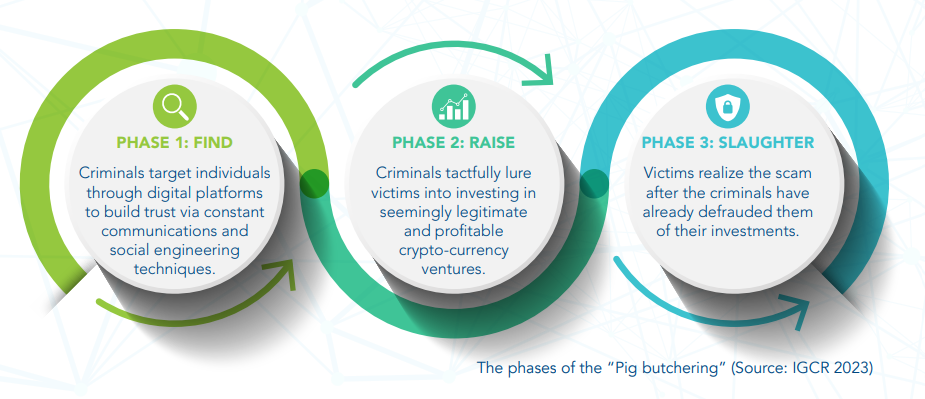
This hybrid scam combines elements of romance fraud and fake cryptocurrency schemes. Victims are lured into trusting scammers who claim to be financial advisors, only to lose substantial investments in fraudulent crypto platforms.
Image depicting the phases of pig butchering:
📌 Role of Internet Governance: Internet governance can address this threat by:
- Advocating for regulations on cryptocurrency exchanges to ensure better transparency and traceability.
- Encouraging ISPs to block access to fake investment platforms and phishing websites.
- Enhancing digital literacy programs to teach users how to spot fraudulent financial offers.
📌 Reader Challenge: Have you encountered suspicious investment opportunities online? Share your experience and how you dealt with it.
The Role of Internet Governance in Tackling Cybercrime
As stated in the INTERPOL report, the internet is the cornerstone of today’s digital economy, but it is increasingly exploited by cybercriminals. Internet governance provides a structured approach to combat these threats by bringing together governments, private sectors, and civil society to establish robust policies, norms, and practices.
How Internet Governance Helps
- Unified Cybercrime Laws: Internet governance facilitates cross-border collaboration to define cybercrimes, standardize penalties, and streamline legal action.
- Strengthened Cybersecurity Ecosystems: It encourages the adoption of technologies like AI for threat detection and multi-factor authentication (MFA) to secure critical systems.
- Education and Advocacy: Governance forums can lead grassroots initiatives to improve digital literacy and promote cyber hygiene across all demographics.
💡Relevance: This approach ensures that nations not only defend against current cyber threats but also anticipate and mitigate future risks.
Recommendations and Way Forward
- Invest in Cybersecurity Technology and Training: African governments and organizations should equip law enforcement with advanced cybersecurity tools and provide specialized training to strengthen local expertise in tackling emerging threats
- Enforce Reporting Mechanisms: Governments should create accessible and efficient cybercrime reporting platforms for businesses and individuals, ensuring timely responses and faster action against threats.
- Encourage Cross-Sector Collaboration: African countries should foster collaboration between governments, tech companies, and civil society to share intelligence and best practices, leveraging partnerships with INTERPOL and @AFRIPOL.
- Expand Digital Literacy Campaigns: Launch national initiatives to educate citizens on recognizing cyber threats and practicing good online security habits, focusing on vulnerable groups like youth, women, and small businesses.
- Strengthen International Cooperation: African nations should enhance coordination through initiatives like the AFJOC and collaborate with global organizations such as INTERPOL to tackle cross-border cybercrime effectively.
Together, we can create a resilient, inclusive, and secure digital environment for Africa and beyond.
(Based on INTERPOL’s African Cyberthreat Assessment Report 2024 and insights from Internet Governance principles)




